This week, RedBear IT moderated a panel discussion webinar on Cloud Security priorities for 2021. The crazy year that is 2020 has been hugely challenging for security professionals with the sudden shift to remote working and the continued increase in cyber attacks. The expert panel reflected on the year. They also discussed their core priorities for 2021 for Cloud Security.
On the panel were
- Tony Wilson, General Manager – Information Security, Latitude Financial Services;
- Braam Broodryk, Head of Security Strategy, Transgrid;
- Brad Flanagan, Head of Cyber Security, Essential Energy.
We also asked a number of questions of our audience during the webinar. We are sharing these results as part of this wrap up.
The Cloud journey
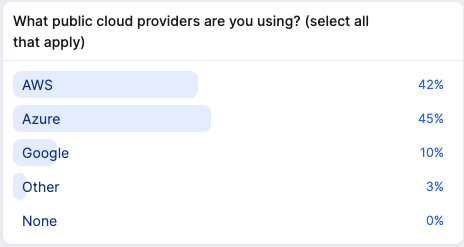
Like our panel, our audience members were all at different stages of their Cloud journey. Nearly everyone told us that they were operating in a hybrid configuration with on-premises and public Cloud environments. The use of SaaS solutions was also common.
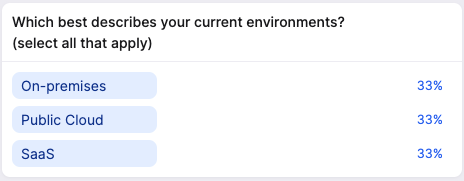
For those that were using the public Cloud, AWS and Azure were clear leaders. While the use of GCP lagged behind the leaders, it has shifted significantly upwards in the last 12 months.
Key themes
Throughout the discussion, the following themes emerged as the most relevant and important to the panel.
Foundations
Even if you are looking at a SaaS solution, it’s important to get the foundations, such as identity, right. Don’t underestimate the importance of defining what you want to achieve. Consider the compliance requirements. Identify the security controls required to support them. Don’t forget how you are going to ensure adherence to these controls. One of the many benefits of Cloud solutions is that you aren’t locked in to a solution. This means you can move quickly and adapt as required. Building foundations is always a balancing act between a sufficient level of planning and getting started. Be careful not to be a roadblock whilst ensuring a level of control and oversight. Guardrails are your friend, not hard rules.
Visibility
Public Cloud solutions offer a huge opportunity for instrumentation. In the box, they provide log information across multiple levels. From audit level, via services such as CloudTrail, to network level logging (at both the metadata and packet level). Having visibility of your Cloud environments should be seen as mandatory.
In late 2017, Gartner ran a survey on the visibility of Cloud environments. Over 80% of responders in that survey expressed that they didn’t believe that they had adequate coverage. Our survey of the audience put that number at 36% which is a fantastic improvement!

One of the challenges in this space is trading off the amount of data you have available versus the cost of analysing and storing that data. No-one wants to make choices about what security data to consume and what to discard!
Cloud security capabilities
Our panelists agreed that migrating or adopting the Cloud bring new security capability opportunities. The Cloud is built around automation through APIs. It has key foundational features in the box. For example, you can enable encryption of storage by default at no cost. As Werner Vogels, the CTO of amazon.com would say, “Dance like nobody is watching, encrypt like everyone is”. Recovery from ransomware is also simpler and quicker through enabling multiple copies of data encrypted with independent keys, all natively supported in the Cloud.
However, it is critical to be aware of the shared responsibility model of the Cloud. Whilst the provider takes care of the security of the Cloud, it is up to your organisation to configure the tools appropriately. S3 buckets are now blocked from public access by default. There were a number of high profile cases a few years ago where data was leaked through wrongly configured S3 buckets. It’s no good having window locks and an alarm on your house if you never use them! Linking back to your foundations and testing and proving your security controls is critical.
Another benefit of the Cloud is that new security capabilities are released all the time. For example, AWS released a new fully managed Network Firewall only two weeks ago. It simplifies the ability to manage your firewall policy as code! Like most of these services, it can be up and running in minutes. This allows you to try it out and then tear it down when you are done. The only cost is the few hours that you run the service. There’s no upfront cost or risk of investing in the wrong solution.
Automation
Security threats and bad actors don’t take a holiday. They are very well resourced. We have seen an increase in general threat activity since the start of the pandemic. So how do you stay on top of the threats? Nobody can afford a floor full of security analysts. Even if you could, would you want to? Could you even find enough appropriate skilled resources? The latest ISC2 study on CyberSecurity Workforce has identified a gap in required security resources of 2.6 million in the APAC region alone!
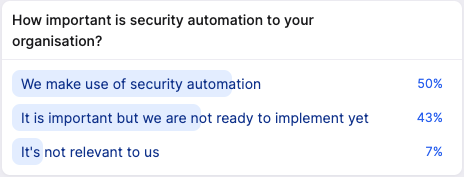
One of the solutions is to make use of automation. Automation in security can be applied to discovery, to compliance reporting and to automated response. Our audience agreed that automation is important as part of their security solution. 93% are already using or are planning to use automation.
Automation allows you to rapidly deal with potential security incidents for which there is a known fix. It allows you to analyse and pick out the needles that matter amongst the tsunami of data. The beauty of applying security automation to the Cloud is that all the hooks are already there to make it happen. At RedBear, we make heavy use of the AWS serverless service, Lambda, as part of our event driven security automation. Even auditing is beginning to be tackled by automation, with the release of the AWS Audit Manager!
Don’t underestimate the power of automating your security testing. This particularly applies to integrating security testing into your CI/CD process. In general, finding security issues earlier in the development lifecycle is far cheaper and quicker to fix than just before launch.
Of course, before you build automation, you need to know that to automate. It’s important to build out and continuously refine your incident response run books. Again, this links us back to getting your foundations right!
Cloud Security Priorities for 2021
So what are our security leaders focussing on for 2021?
Dealing with the volume of data without losing security insights is seen as a key outcome for 2020. With pressure on cost to income, automation will be key to improving the efficiencies of processes and of response. Using analytics across security data will allow resources to focus on the most important and relevant vulnerabilities and incidents.
However, this requires a focus on not just getting the right tools in place but also tuning those tools for your environments. This should be driven by your business environment, including compliance and standards to which you may need to conform. Remember that it’s not a one time activity! You will need to continuously refine your controls and your associated tooling!
Actions for your organisation
If you are already in the public Cloud, we recommend reviewing your security posture.
- Consider you risk and compliance requirements and review your controls;
- Review your visibility solution;
- Do you have the coverage and targeted alerts that you need?
- Consider automating you incident response if you haven’t done so already.
For those early in the Cloud journey,
- Identify your business goals;
- Define your foundations around identity, compliance, development and deployment to name a few;
- Set some standards and guardrails so your security teams can enable, not hinder, your business;
- Start building, measure and refine;
- Don’t forget the visibility of your environments. After all, it is impossible to improve upon something without measuring it first!
Finally, in 2021, one thing that won’t change is the most common source of security breaches. Unfortunately, it’s us humans. Phishing attacks and weak password continue to plague organisations and personal accounts. Educate your teams. Consider running phishing simulations. Ensure that you enforce strong passwords and MFA.
If you would like to progress your Cloud Security journey or understand your Cloud security priorities for 2021, please get in contact with us. Let work together to help your organisation stay safe on Cloud!